Summary:
- A phishing campaign is targeting developers by exploiting OpenClaw's growing popularity.
- Attackers are using fake GitHub accounts and "$5,000 CLAW token" giveaways to lure victims.
- Victims are redirected to a cloned OpenClaw website that prompts wallet connection to steal funds.
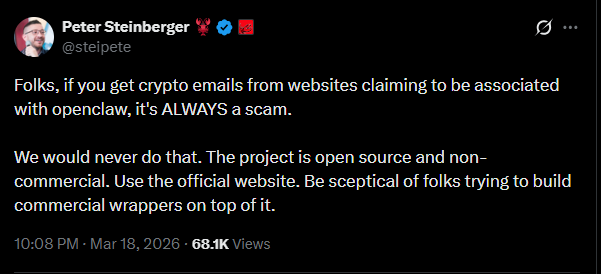
- OpenClaw creator Peter Steinberger warned that any crypto-related outreach tied to the project is a scam.
- Cybersecurity firm OX Security identified malicious domains and wallet addresses linked to the attack.
As OpenClaw continues to gain attention among developers, attackers are moving just as fast. A new phishing campaign is now using the project's name to trick users into giving away access to their crypto wallets. Cybersecurity firm OX Security revealed that threat actors have been creating fake GitHub accounts and opening issue threads in repositories they control. From there, they tag developers and claim they've been selected for a reward - usually framed as $5,000 worth of "CLAW" tokens. At first glance, it looks like a normal developer interaction. GitHub issues, tagged users, and reward claims aren't unusual in open-source communities. That's exactly why the tactic works. Once clicked, victims are taken to a website that looks almost identical to OpenClaw's official page. The layout, branding, and structure are nearly the same. There's just one extra element that shouldn't be there - a "Connect your wallet" button.

That single button is where everything changes. Instead of claiming rewards, users who connect their wallets unknowingly grant access to malicious scripts designed to drain funds. According to OX Security, the phishing page supports several popular wallets, including MetaMask, Trust Wallet, WalletConnect, OKX Wallet, and Bybit Wallet. The attack doesn't stop at GitHub. OX noted that the campaign also spreads through email outreach, often disguised as tools or extensions related to the OpenClaw ecosystem. This adds another layer of credibility, making it harder for users to spot the trap early. The scale of the campaign is still unclear, but the structure suggests a coordinated effort and more depth.
READ MORE : MEV Bot Nets $9.9M After $50M AAVE Swap Goes Wrong, User Receives Only $36K
How the Attack Works Behind the Scenes
What makes this phishing campaign more concerning is how it's built under the hood. The malicious code is intentionally hidden and difficult to detect. OX Security found that the wallet-draining logic is embedded inside a JavaScript file named "eleven.js."
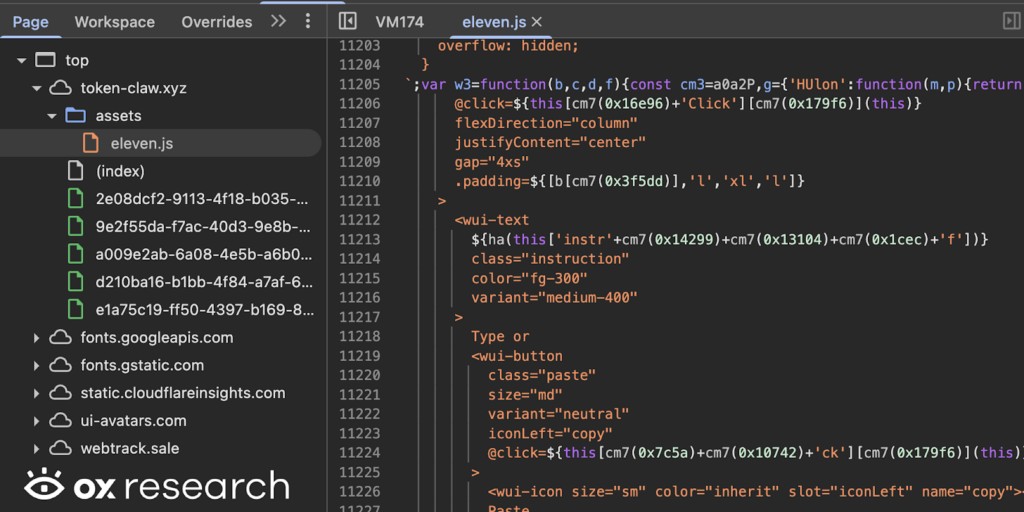
The code is heavily obfuscated, meaning it's scrambled in a way that hides its true function from anyone casually inspecting it. This is a common tactic in more advanced phishing setups. Instead of obvious red flags, the attack relies on subtle execution after the user takes action. Once the wallet is connected, the script can trigger unauthorized transactions or approvals in the background. Many users won't realize what's happening until funds are already gone. OX researchers also identified a wallet address believed to be linked to the attacker:
To reduce exposure, OX advised users to block known malicious domains such as token-claw[.]xyz and watery-compost[.]today, and to treat any GitHub issue promoting token giveaways with caution. The structure of the attack shows a clear pattern seen across crypto-related scams. Attackers are targeting behavior - curiosity, urgency, and the appeal of free tokens.
Rising Popularity Brings New Risks for OpenClaw Users
The timing of this campaign isn't random. It closely follows OpenClaw's rapid rise within the developer community. The project has crossed 324,000 stars on GitHub, placing it among the top repositories globally. That level of visibility naturally attracts attention, not just from developers, but also from attackers looking for easy entry points.
There's also been a boost in exposure after OpenClaw creator Peter Steinberger joined OpenAI last month. While the project continues to operate under an independent open-source foundation, the added spotlight has made it a more attractive target. Steinberger has already stepped in to warn users about the situation. In a public message, he made it clear that any crypto-related promotion tied to OpenClaw should be treated as a scam:
As open-source projects grow, unofficial tools, wrappers, and third-party offers tend to appear around them. Not all of them are harmful, but some are designed purely to exploit trust. For developers and users, the takeaway is simple but important. Even in trusted environments like GitHub, not everything is safe by default. A familiar interface doesn't guarantee a legitimate interaction. The phishing campaign may evolve, new domains may appear, and different tactics may be used. But the core pattern will likely stay the same - using trust and visibility as the entry point. However in crypto, a single click is often all it takes.
READ MORE: SEC Drops Case Against Justin Sun After $10M Settlement, Closing Three-Year Crypto Lawsuit