Summary:
- Crypto e-commerce firm Bitrefill disclosed a cyberattack on March 1, 2026, likely linked to North Korea's Lazarus Group.
- Attackers accessed around 18,500 purchase records, exposing limited customer data.
- Some of Bitrefill's hot wallets were drained, with funds moved to attacker-controlled addresses.
- The breach reportedly began through a compromised employee laptop.
- Bitrefill has taken systems offline and is working with security experts and law enforcement to investigate.
Crypto e-commerce platform Bitrefill has revealed it was targeted in a cyberattack earlier this month, with early findings pointing toward the involvement of North Korea's Lazarus Group, a well-known hacking collective tied to multiple attacks in the crypto sector. The company shared details of the incident in a public update, outlining how the attack unfolded and what has been uncovered so far. According to Bitrefill, the breach took place on March 1, 2026, and showed patterns similar to previous attacks linked to Lazarus and its subgroup, Bluenoroff. In its official statement, Bitrefill said:
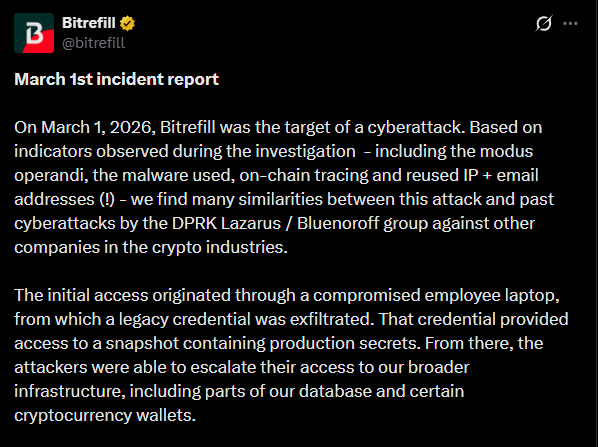
The company stopped short of making a definitive attribution, but the overlap in attack patterns, infrastructure, and behavior has raised strong suspicions among investigators. The Lazarus Group has been linked to several major crypto-related breaches over the past few years, often targeting exchanges, wallets, and infrastructure providers. These attacks typically involve sophisticated phishing methods, malware deployment, and careful tracking of on-chain funds. Bitrefill noted that the breach appears to have originated from a compromised employee laptop, a method that aligns with known tactics used by Lazarus-linked operations.
READ MORE: Trump Cyber Strategy Puts Crypto and Blockchain Security at Center of U.S. Tech Leadership
Customer Data Accessed and Funds Moved
As part of the breach, attackers were able to access approximately 18,500 purchase records. While the company emphasized that the exposed data was limited in scope, it still included sensitive metadata such as email addresses, crypto payment addresses, and IP-related information. Bitrefill clarified the nature of the data exposure, stating:
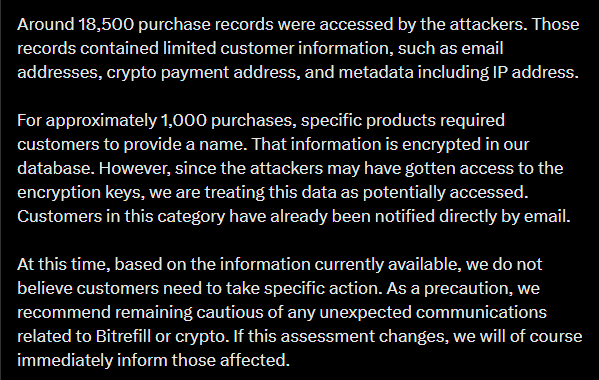
Although the company highlighted that certain personal details were encrypted, the exposure of transaction-related data still raises concerns for users, particularly in a space where privacy is often a key priority. Beyond data access, the attackers were also able to exploit parts of Bitrefill's operational infrastructure. According to the company, gift card inventory and supply systems were manipulated during the incident, allowing unauthorized purchases to take place. At the same time, some of Bitrefill's hot wallets-wallets connected to the internet and used for day-to-day transactions-were drained, with funds transferred to addresses controlled by the attackers. Once the breach was identified, Bitrefill acted quickly by taking its systems offline to contain the damage and prevent further unauthorized activity. The company has since been working with a range of external experts, including security researchers, incident response teams, and blockchain analysts, to investigate the attack and trace the movement of funds. It also confirmed cooperation with law enforcement as part of the ongoing response.
READ MORE : MEV Bot Nets $9.9M After $50M AAVE Swap Goes Wrong, User Receives Only $36K
A Familiar Pattern in Crypto Attacks
The Bitrefill incident adds to a growing list of cyberattacks targeting crypto-related companies, many of which have been linked to state-sponsored groups. The Lazarus Group, in particular, has developed a reputation for targeting digital asset platforms. Its operations often focus on exploiting human vulnerabilities-such as phishing emails or compromised devices-rather than directly breaking cryptographic systems. In this case, the suspected use of a compromised employee device highlights a recurring theme in cybersecurity: even well-protected systems can be exposed through individual access points. Once attackers gain entry, they typically move laterally within a network, identifying valuable assets such as wallets, internal systems, or databases. From there, they execute transactions and attempt to obscure the trail using multiple wallet addresses and blockchain movements.
The exposure of purchase records in the Bitrefill case also reflects another common risk. While blockchain transactions themselves are transparent, the services built around them often store user data that can become a target during breaches. For users, incidents like this serve as a reminder to remain cautious about sharing personal information and to follow basic security practices, such as using unique email addresses and enabling additional layers of account protection where possible. For companies, the attack underscores the importance of securing also endpoints like employee devices that can serve as entry points for attackers. Bitrefill's response-taking systems offline, engaging external experts, and publicly disclosing details-follows a growing trend of transparency in the crypto industry when dealing with security incidents.
Closing Thoughts
While the full scope of the financial impact has not yet been disclosed, the investigation is ongoing, and further updates are expected as more information becomes available. As crypto adoption continues to expand, so too does the attention from sophisticated threat actors. Incidents like this highlight the ongoing challenge of balancing accessibility, speed, and security in a fast-moving digital asset ecosystem.
READ MORE : UK Man Claims Wife Used CCTV Footage to Steal $176M in Bitcoin From Hardware Wallet, Court Told