Summary:
- Vitalik Buterin has outlined a roadmap to make Ethereum resistant to future quantum computer threats.
- Four vulnerable areas were identified: validator signatures, data availability, user account signatures and zero-knowledge proofs.
- The plan includes replacing BLS and ECDSA signatures, moving away from KZG commitments, and introducing recursive proof aggregation.
- While technically possible, the shift will require deep engineering work and careful design choices that could shape Ethereum for decades.
Quantum computing has long been discussed as a distant risk to blockchains. But as research accelerates and powerful machines move from theory toward practical reality, developers are beginning to treat the issue as a serious long-term challenge. This week, Ethereum co-founder Vitalik Buterin laid out a detailed roadmap describing how the network could defend itself against quantum threats. His proposal focuses on four parts of Ethereum that he believes are most exposed today. In his words:
" Today, four things in Ethereum are quantum-vulnerable:
- consensus-layer BLS signatures
- data availability (KZG commitments+proofs)
- EOA signatures (ECDSA)
- Application-layer ZK proofs (KZG or groth16) "
Buterin described a phased approach that touches the very foundations of how Ethereum verifies transactions, stores data, and validates cryptographic proofs.
Rethinking Validator Signatures and Hash Functions
One of the most immediate concerns lies in Ethereum's consensus layer. Validators currently use BLS signatures to confirm blocks and secure the chain. These signatures are efficient and elegant, but they rely on cryptographic assumptions that could break under a sufficiently advanced quantum computer. Buterin suggests replacing them with hash-based signature schemes, potentially variants of Winternitz signatures. These are considered quantum-resistant because they rely on hash functions instead of elliptic curve cryptography.
He notes that Ethereum may adopt a "Lean" approach to consensus, which would involve fully replacing BLS and using STARK-based aggregation techniques where necessary. However, before that transition is complete, a more limited setup with fewer signatures per slot could reduce complexity. A major upstream decision involves selecting a hash function that will likely remain part of Ethereum's core design for decades. As Buterin put it: "This may be 'Ethereum's last hash function', so it's important to choose wisely." Conventional hash functions may be too slow for Ethereum's needs, while some newer cryptographic designs have faced recent review. Options under consideration include updated versions of Poseidon or more traditional high-performance hashes like BLAKE3.
Data Availability: Moving Beyond KZG
Ethereum's current data availability system relies heavily on KZG commitments. These cryptographic tools allow the network to verify that large pieces of data, often referred to as blobs, are correctly formed without downloading everything. However, KZG is not quantum-resistant. The proposed alternative is STARK-based proofs. STARKs are widely seen as secure against quantum attacks because they rely on hash-based constructions rather than elliptic curves. Ethereum's current roadmap includes techniques like data availability sampling that depend on certain mathematical properties of KZG commitments. STARKs do not naturally provide the same structure, which complicates scaling plans. Buterin summarized the situation clearly:
In practice, this means Ethereum may lean toward simpler scaling targets rather than pushing to become an ultra-high-throughput data layer. The shift to STARK-based systems will require rethinking how blobs are constructed, verified, and distributed across the network.
User Accounts and the End of ECDSA
Ethereum user accounts today rely on ECDSA signatures, the same cryptographic standard used in Bitcoin and many other systems. Like BLS, ECDSA is vulnerable to quantum attacks. The fix, according to Buterin, is native account abstraction. By implementing proposals such as EIP-8141, Ethereum could allow accounts to use any signature scheme. This flexibility would open the door to quantum-resistant signatures, including hash-based and lattice-based systems. The challenge is cost, current ECDSA verification consumes about 3,000 gas. Quantum-safe alternatives can cost hundreds of thousands of gas to verify.
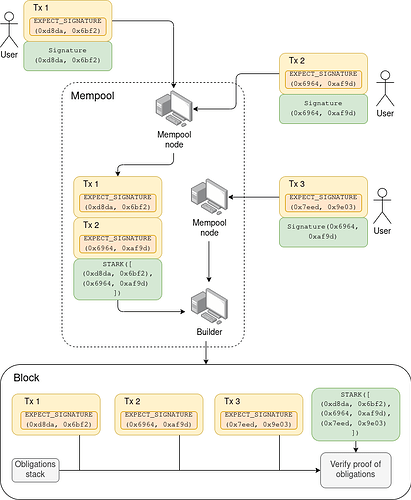
That difference would make normal transactions dramatically more expensive. To address this, Buterin points to aggregation at the protocol level. Ethereum could bundle many signatures into a single proof that confirms all of them at once.
If successful, this would preserve user experience while fundamentally upgrading the network's cryptographic backbone.
The High Cost of Quantum-Resistant Proofs
Zero-knowledge proofs are another cornerstone of Ethereum's ecosystem, especially for privacy tools and layer-2 scaling networks. Today's SNARK-based proofs already cost hundreds of thousands of gas to verify. Quantum-resistant STARK proofs can cost dramatically more. That level of expense would be unsustainable for privacy applications and rollups.
Buterin's answer again centers on recursive aggregation. Ethereum could verify a single master proof that confirms thousands of underlying operations. He explained the concept this way:
In simple terms, heavy computation would happen offchain, while Ethereum would only process compact proofs confirming everything was done correctly. Over time, this could shift much of the network's verification burden away from raw computation and toward proof verification.
A Long Road Ahead for Ethereum
However, Large-scale quantum computers capable of breaking Ethereum's cryptography do not yet exist. But preparing early gives the ecosystem time to test, debate and refine its approach. What stands out in Buterin's roadmap is its realism. He does not claim the transition will be simple. Each component touches deeply embedded parts of Ethereum's design. Hash function choices, data verification structures and signature formats all influence performance, cost and decentralization.
If implemented successfully, these changes could future-proof Ethereum against one of the most serious theoretical threats facing public blockchains. More importantly, the roadmap shows that Ethereum's leadership is thinking decades ahead. Quantum computing may still be years away from disrupting cryptography at scale. But Ethereum's plan suggests the network intends to be ready long before that moment arrives.
READ MORE: Vitalik Said "Build Something New." COTI Already Did