Summary:
- Garbled Circuits (GC) are a cryptographic method used in secure multi-party computation (MPC).
- They allow multiple parties to compute a result together without revealing their private inputs.
- The concept originated from Andrew Yao's 1982 "Millionaire's Problem."
- GC is considered one of the most important building blocks in modern privacy-preserving cryptography.
- Recent research from universities such as Oxford shows ongoing advances in performance, flexibility, and security, expanding how GC can be used in real-world systems.
Modern digital systems constantly process sensitive information like financial records, health data, business strategies, and personal identities are all handled by software that must deliver results without exposing confidential details. But still, traditional computing models struggle with this balance. Normally, systems must access raw data to compute results, which creates risks around privacy, leaks, or misuse. Cryptography has been searching for a better approach to perform useful computation without revealing the underlying data. This challenge led to the development of secure multi-party computation (MPC), a field of cryptography focused on enabling multiple participants to jointly compute a function while keeping their inputs private.
One of the most influential techniques within MPC is Garbled Circuits (GC). In simple terms, Garbled Circuits allow a program to run on encrypted inputs. The program produces a valid output, but the underlying data remains hidden throughout the process. This makes GC a powerful tool for situations where privacy is essential but collaboration is required. The foundation/concept was first introduced in 1982 by computer scientist Andrew Yao through a thought experiment known as the Millionaire's Problem.
Today, Garbled Circuits are widely studied by cryptographers and researchers, with ongoing work expanding their efficiency and real-world applications.
The Famous "Millionaire's Problem"
The easiest way to understand Garbled Circuits is through the scenario that inspired them. Imagine two wealthy individuals who want to know who is richer. Neither person wants to reveal their exact wealth to the other, but they still want to determine which one has more money. This problem highlights a common challenge that computing a result while keeping inputs private. Andrew Yao proposed a cryptographic solution in 1982. Without revealing their wealth, both parties could input their values into a special encrypted computation system. The system would perform the comparison internally and reveal only the final answer like who is richer without exposing the original numbers.
This idea eventually evolved into the concept of Garbled Circuits. This approach became an advanced model of secure multi-party computation research. Today, the Millionaire's Problem is still widely used as a teaching example, but the underlying idea now powers much more complex systems including privacy-preserving financial analysis, secure auctions, machine learning, and blockchain-based computation.
How Garbled Circuits Work (Without the Math)
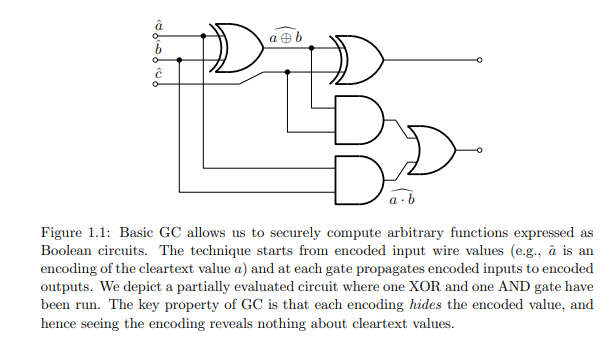
To better understand the concept, imagine turning a computer program into a locked machine. Normally, a program takes input, processes it, and produces output. In the case of Garbled Circuits, the program itself is encrypted before it is shared with another party. The process usually happens in two steps. First, one participant encrypts the program. Every component of the computation - each logical operation in the circuit - is transformed into a "garbled" version that hides its internal logic. Second, the other participant runs the encrypted program using encrypted inputs. Even though the program executes normally, the underlying data never appears in plaintext.
The result is a correct output, but none of the intermediate steps are visible. Researchers often describe this as evaluating a Boolean circuit under encryption. In computing, Boolean circuits represent programs using logical operations like AND, OR, and NOT. Garbled Circuits convert these operations into encrypted equivalents. This technique enables multiple parties to collaborate securely without exposing sensitive information.
What Makes Garbled Circuits Powerful
One reason Garbled Circuits remain widely studied is because they provide several advantages compared with other privacy technologies. Their design is relatively lightweight compared with some advanced cryptographic techniques. Many implementations rely mainly on symmetric encryption, which modern processors handle very efficiently. As a result, Garbled Circuits can often run on standard computers without requiring specialized hardware. They are also known for their speed. Some privacy technologies such as Fully Homomorphic Encryption allow extremely powerful encrypted computation but can be computationally heavy. Garbled Circuits tend to avoid those performance bottlenecks and make them faster in many cases.
Security is another strength. Because the inputs remain encrypted throughout the process, sensitive information is never directly exposed during computation. Flexibility also plays an important role. Garbled Circuits can support collaborative computation between multiple participants who each contribute different inputs. Researchers often emphasize how central this technique has become within cryptography. According to “New Directions in Garbled Circuits” research paper says:
David Anthony also highlights several key concepts, including Garbled Circuit Construction, Free XOR, Half-Gates, Garbling Notation, Stacked Garbling, and Garbled RAM. He also explains why Garbled Circuits continue to appear in modern privacy research and remain relevant in confidential computing.
The Garbling Process Explained
At the technical level, Garbled Circuits rely on a process called garbling, which transforms a normal program into an encrypted version.
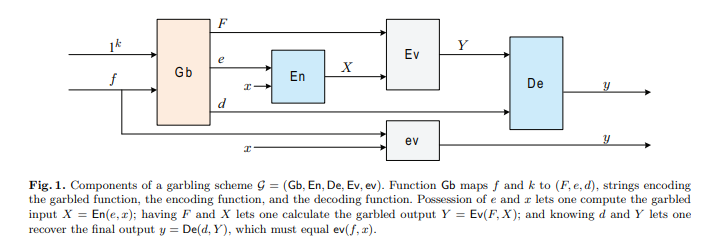
Researchers describe this process using three major components: encoding, evaluation, and decoding. First, an encoding function converts a user's input into encrypted values and the system works with encrypted representations. Next, the garbled program evaluates the encrypted input. This stage produces a garbled output of an encrypted result that corresponds to the original computation. Finally, a decoding function converts the encrypted result into the final output that users can read. In simplified terms, the process can be described as: Encode → Compute → Decode
Mathematically, researchers often describe it as breaking a function into three stages so that the original computation can be reconstructed without exposing internal data. This structure allows encrypted computation to behave exactly like normal computation, except that the inputs remain hidden. Detailed technical descriptions of this process appear in cryptography research papers and formal security proofs.
Two-Party Computation and Secure Function Evaluation
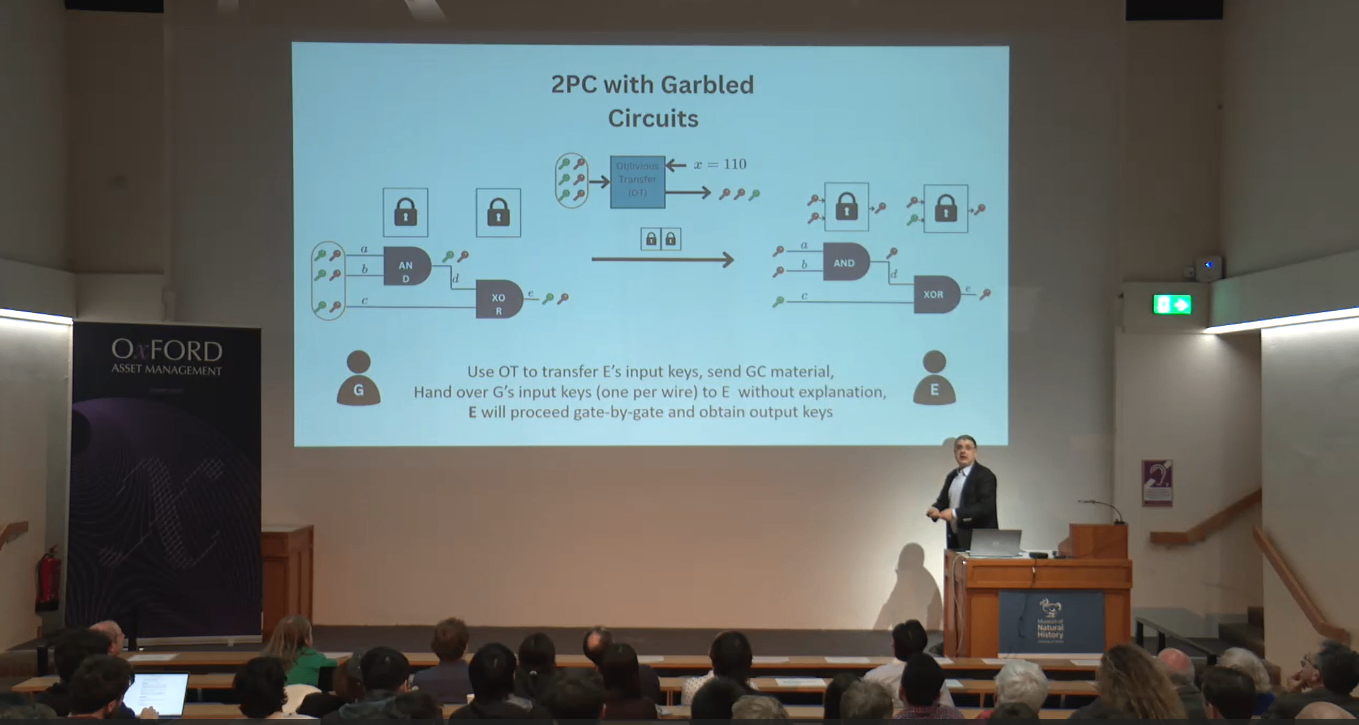
Garbled Circuits are most commonly used in two-party secure computation, often called 2PC. In this setting, two participants each have private inputs. They want to compute a function that depends on both inputs, but neither wants to reveal their own data.
A typical protocol works roughly like this, One participant constructs a garbled version of the circuit representing the function to be computed. They send the garbled circuit to the other participant along with encrypted input keys. The second participant obtains the keys corresponding to their own input through a cryptographic method called oblivious transfer, which ensures they receive the correct key without revealing their data.
Once the inputs are prepared, the second participant evaluates the garbled circuit and obtains the final output. Importantly, the evaluation reveals only the output of the computation, nothing about the private inputs themselves. This method allows secure collaboration between parties that may not fully trust each other.
Recent Advances in Garbled Circuits
While Garbled Circuits originated decades ago, research in this area continues to evolve. One recent area of study focuses on improving efficiency and expanding the types of programs that can be evaluated securely. Professor Rafail Ostrovsky, a leading cryptography researcher, has explored several advancements in garbling schemes during the Oxford Series “Strachey Lectures”. His work surveys modern techniques that extend the original concept into more flexible computation models. One example is Garbled Random Access Memory (GRAM), introduced by Lu and Ostrovsky in 2013. GRAM allows encrypted programs to access memory in ways that resemble normal computing environments. This development significantly expanded the types of programs that can be evaluated securely using garbled techniques.
Further progress has been made in optimizing these systems for practical deployment. Research by Heath, Kolesnikov, and Ostrovsky received the best paper award at Eurocrypt 2022 for advancing GRAM-related designs. Another major research direction involves strengthening security in adversarial environments. In real-world systems, participants may attempt to deviate from protocols to gain additional information. Modern garbling schemes aim to maintain security even when participants behave maliciously.
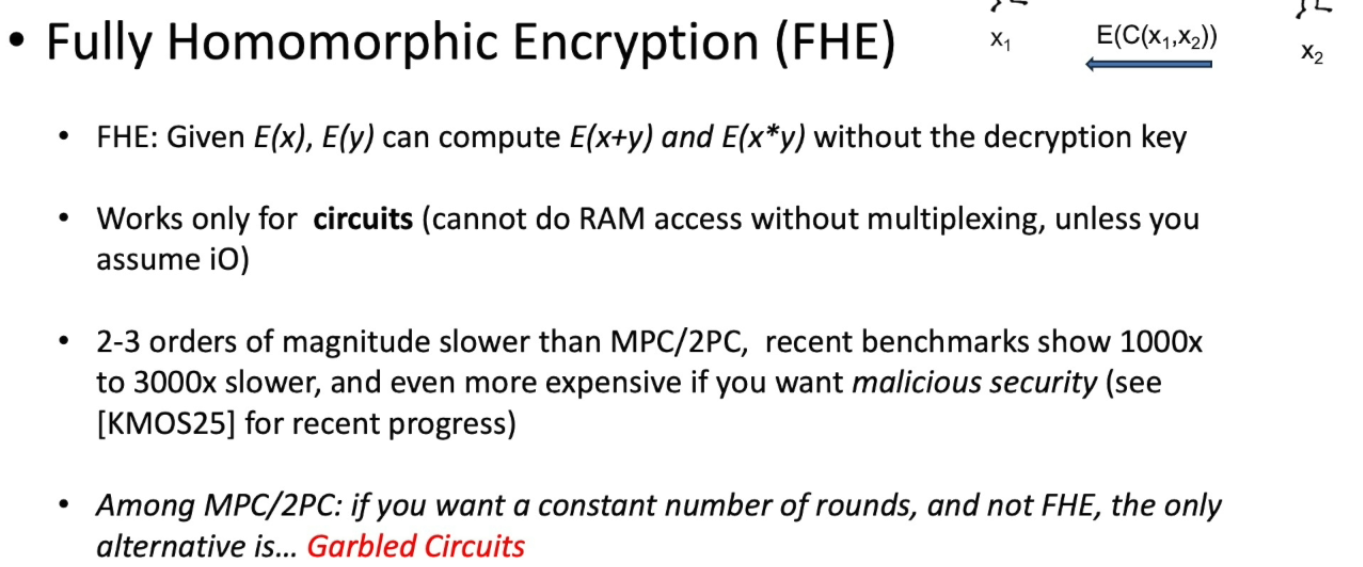
Professor Rafail Ostrovsky, in his Oxford lecture series on October 27, 2025, shared an infographic from recent research claiming that benchmark results show Fully Homomorphic Encryption (FHE) can be around 1000x to 3000x slower and significantly more expensive. He also noted that "if you want a constant number of rounds and prefer and not FHE, the only alternative is Garbled Circuits". Professor Rafail Ostrovsky, in his Oxford lecture series, explains about garbling, two-party computation (2PC) with garbled circuits, and the introduction of Garbled Random Access Memory (GRAM) and some more key things. You can check the video to gain a deeper understanding of these topics and how they relate to modern privacy-preserving computation.
Why Garbled Circuits Matter for the Future of Privacy
Privacy-preserving computation is becoming increasingly important as digital systems grow more complex. Organizations want to collaborate without exposing proprietary data, governments need systems that process sensitive information without risking leaks, financial platforms must protect trading strategies while maintaining transparency in settlement. Garbled Circuits offer a path toward solving these challenges.
So, Instead of forcing users to choose between privacy and collaboration, encrypted computation allows both at the same time. Data can remain confidential while still producing verifiable outcomes. This capability has implications across many industries, including finance, healthcare, identity systems, and decentralized technologies. As research continues and implementations improve, Garbled Circuits are likely to remain a core component of the privacy-preserving computing landscape. Garbled circuits have evolved into one of the most influential tools in secure computation and its development is still ongoing.