Summary:
- Drift has sent onchain messages to wallets tied to the $280M exploit
- The team is trying to open direct communication with the attacker
- An unknown sender also contacted the wallets, demanding 1,000 ETH
- Over 20 Solana protocols are now affected by the fallout
- Speculation around attacker identity remains unconfirmed
Drift is now trying a different approach following the $280 million exploit - direct communication with the wallets holding the stolen funds. The Solana-based trading platform confirmed that it has initiated contact onchain, sending messages from its Ethereum address to wallets linked to the attacker. The goal is to communicate and see if any form of resolution is possible. At the time of writing, Drift has reached out to four wallets connected to the exploit. The message was sent through Ethereum-based tools that allow wallet-to-wallet communication without revealing identities. "We are ready to speak," the team said, inviting the attacker to respond through Blockscan chat.

This method has started to show up more often after major exploits. Instead of relying only on exchanges or law enforcement, teams are using onchain messaging to reach attackers directly. It keeps everything visible onchain while still allowing both sides to stay anonymous. In earlier cases like the Euler Finance incident, similar outreach played a role in recovering part of the stolen funds. It doesn't always work, but it creates a channel where there was none. For Drift, this move suggests they are exploring every possible path, with continuously tracking funds and also trying to engage with whoever is behind the wallets.
A Second Message Adds Pressure
Around the same time, an unknown sender using the ENS name readnow.eth also contacted the same wallets. But the tone was very different. According to available information, this sender claimed to know the identities behind the exploit and demanded a payment of 1,000 ETH in exchange for keeping that information private. There's no confirmation that these claims are real. It could be an attempt to pressure the attacker or simply create confusion around the situation. But things get messy after a large exploit. Once wallet addresses are known, anyone can send messages. Some may be genuine attempts to resolve the issue, others may not.
This creates a strange dynamic where multiple parties try to interact with the same wallets, all with different intentions. For observers, it becomes harder to separate signal from noise.
Fallout Spreads Across Solana
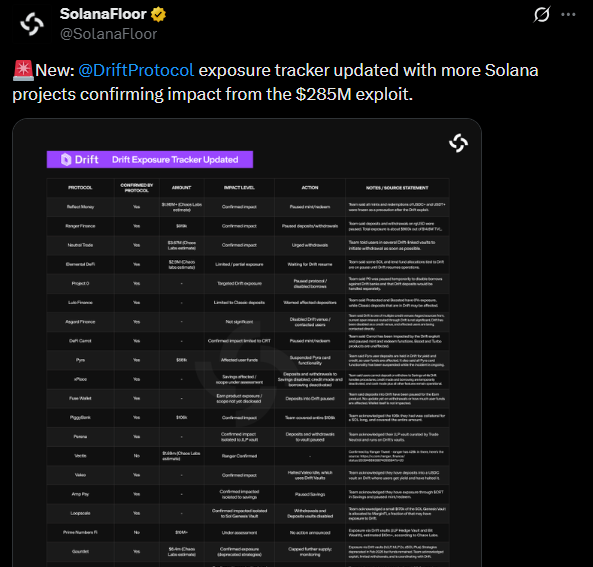
The impact of the exploit is no longer limited to Drift alone. According to updates shared by SolanaFloor, at least 20 Solana-based protocols have now reported some level of exposure. One example is the DeFi platform Gauntlet, which is estimated to have taken a hit of around $6.4 million. The situation is still evolving as more teams assess their exposure and share updates. Each new confirmation adds another layer the effects have spread across the ecosystem. SolanaFloor summarized the growing list of affected projects:
This kind of ripple effect isn't new in DeFi, but when a core protocol is hit, it often affects other platforms connected through liquidity, integrations, or shared infrastructure. There's also early speculation around who might be behind the attack. Charles Guillemet, chief technology officer at Ledger, suggested the possibility of North Korea-linked actors being involved. That said, nothing has been confirmed so far. These claims remain speculative, and no official attribution has been made.
Where Things Stand Now
Drift's decision to initiate onchain communication shows how response strategies are evolving. It's not just about tracking funds anymore - it's also about opening dialogue, even in uncertain situations like this. At the same time, the appearance of outside messages trying to pressure the attacker adds another layer of complexity. It highlights how public and unpredictable these situations can become once they unfold onchain.
The broader impact is still unfolding across Solana, with more protocols stepping forward to report exposure. And while theories about the attacker continue to circulate, the focus remains on recovery and understanding how this happened. For now, one thing is clear. The story isn't over yet - and what happens next may depend on whether that message gets a reply.
READ MORE: Trump Cyber Strategy Puts Crypto and Blockchain Security at Center of U.S. Tech Leadership