Summary:
- THORChain contributors shared a fresh update on the network incident linked to a suspected $10 million exploit.
- Early findings point to a newly churned node potentially linked to a single malicious operator.
- Investigators believe the attacker may have exploited a weakness in GG20 TSS key-sharing infrastructure to reconstruct vault key material.
- The network remains partially paused while recovery discussions continue.
- THORChain later warned users about fake refund websites, fake airdrop claims and impersonator accounts spreading false information.
- THORChain says no official refund, airdrop or compensation program exists, and initial findings suggest user funds were not lost.
THORChain is working through one of its most closely watched security incidents in recent months after contributors published new findings tied to a suspected exploit that temporarily disrupted network activity and raised fresh concerns around decentralized infrastructure security. The update, shared through THORChain's development channels and later circulated publicly, outlined what investigators currently believe happened. According to contributors, current evidence points toward a newly churned validator node potentially linked to the incident. Developers say blockchain analysis has identified connections between Ethereum wallets used to acquire and bond RUNE for that node and wallets that later received suspicious outbound transfers. While the investigation is still ongoing, contributors believe the activity was likely carried out by a single malicious operator. The technical explanation centers on THORChain's GG20 threshold signature scheme implementation - a cryptographic system designed to split private key authority across multiple validators rather than allowing one party to control vault funds.
Investigators say the leading theory is serious enough to explain how unauthorized outbound transactions may have occurred. As the Thorchain team explained:
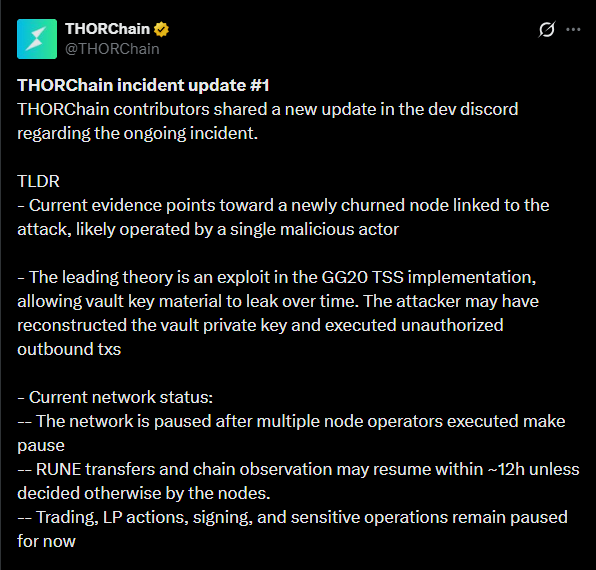
That matters because threshold signature systems are meant to prevent exactly this type of failure. Instead of one private key sitting in one location, pieces of key material are distributed among trusted participants. If enough information leaks gradually, however, reconstruction becomes possible. That appears to be what investigators are now focused on. The discovery triggered an immediate response from validators across the network. As multiple node operators executed emergency pause commands, THORChain entered a temporary network pause state to contain any further risk while investigators assessed damage and discussed recovery options. According to official statement from the team "Due to multiple node operators executing make pause, the network is currently paused. Unless further action is taken, the pause state will automatically expire in approximately 12 hours" The team later clarified the current operational state:
That means some network observation activity may gradually return, but key transactional functions remain suspended until validators agree on next steps. Recovery will likely involve governance coordination. Possible solutions include slashing validator bonds tied to affected vaults or allowing protocol-owned liquidity to absorb part of the impact. No final decision has been made. Contributors acknowledged that bringing THORChain fully back online will not happen overnight. According to the announcement:
For now, security teams, including THOR and blockchain forensic specialists at Outrider Analytics, continue collecting evidence while coordinating with relevant law enforcement agencies.
READ MORE: Bitrefill Hack Linked to Lazarus Group: 18,500 Records Exposed and Hot Wallets Drained
Fake Refund Claims Spread as Impersonators Exploit Confusion
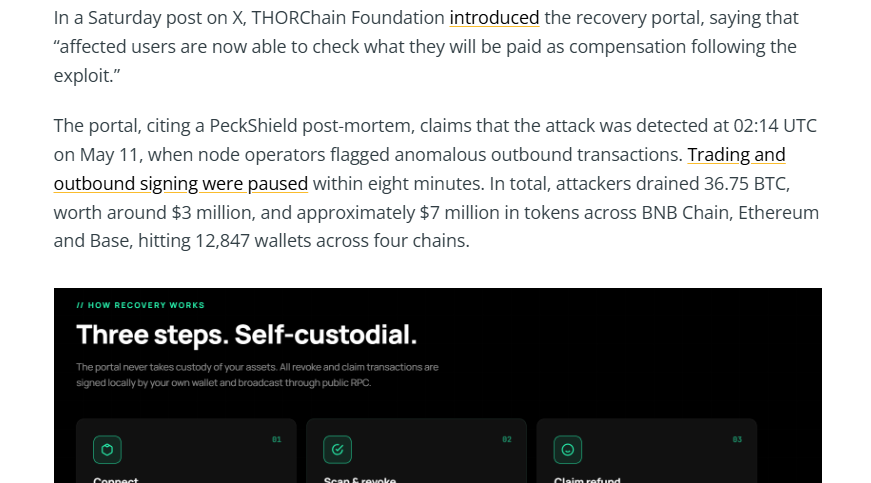
As often happens during major crypto security incidents, misinformation appeared almost immediately. Shortly after the initial incident update circulated, fake social media accounts and fraudulent websites began promoting false claims about THORChain compensation programs. Some impersonator accounts claimed users could connect wallets to receive refunds. Others promoted fake airdrops or compensation portals pretending to represent official recovery efforts. The spread became significant enough that THORChain issued a second public warning directly addressing the misinformation campaign. The Thorchain stated:
Periods of uncertainty often create ideal conditions for scammers. Users looking for updates may be more likely to click unfamiliar links or trust accounts that appear official at first glance. THORChain's statement confirmed there is no active compensation portal and no refund claim process underway. Any site suggesting otherwise should be treated as malicious. This issue reportedly grew large enough that even major crypto media outlets accidentally amplified false claims before corrections were made.
Source: Cointelegraph
Independent investigation by the CotiNews team found some fake links had circulated widely across crypto social channels, adding to confusion around the real incident status. The COTINews team noticed that a Cointelegraph author mistakenly promoted a fake X account and a fraudulent recovery portal in an article. Our team has already reached out to the Cointelegraph team to make them aware of this issue.
That kind of misinformation often spreads faster than official updates, particularly when communities are waiting for answers. For users, the safest move remains simple. Ignore all unsolicited compensation links and rely only on THORChain's verified channels for network updates.
A Wider Security Wake-Up Call for DeFi
THORChain's incident arrives during one of the harshest periods for crypto security in recent memory. April alone saw $629.7 million in crypto-related losses, making it the industry's worst month since February 2025, when hacks exceeded $1.47 billion. Two exploits drove most of that damage. KelpDAO's $293 million exploit and Drift Protocol's $280 million breach together accounted for more than 80% of total losses. Attackers are increasingly targeting infrastructure layers - validator systems, privileged operational access, bridge security models and key management frameworks. That appears consistent with what THORChain investigators are now examining. The incident may ultimately become another reminder that decentralized systems are only as secure as their most complex underlying coordination mechanisms.
THORChain has weathered serious pressure before and historically recovered through rapid community coordination. This time will test that resilience again. The coming days will show whether validators can align around a repair strategy quickly enough to restore confidence. For now, The investigation continues and the network is stabilizing. Also users should ignore anyone promising refunds that do not exist.
READ MORE : MEV Bot Nets $9.9M After $50M AAVE Swap Goes Wrong, User Receives Only $36K